1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
| def calculate_crc64_direct(data):
crc = 0xFFFFFFFFFFFFFFFF
poly = 0x42F0E1EBA9EA3693
for byte in data:
crc ^= (byte << 56) & 0xFFFFFFFFFFFFFFFF
for _ in range(8):
if (crc & 0x8000000000000000) != 0:
crc = ((crc << 1) & 0xFFFFFFFFFFFFFFFF) ^ poly
else:
crc = (crc << 1) & 0xFFFFFFFFFFFFFFFF
return (~crc) & 0xFFFFFFFFFFFFFFFF
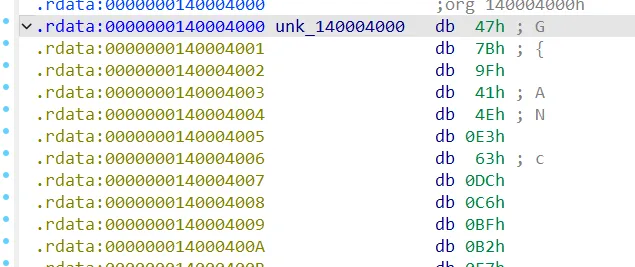
cipher_bytes = bytes([
0x47, 0x7B, 0x9F, 0x41, 0x4E, 0xE3, 0x63, 0xDC, 0xC6, 0xBF, 0xB2, 0xE7, 0xD4, 0xF8, 0x1E, 0x3,
0x9E, 0xD8, 0x5F, 0x62, 0xBC, 0x2F, 0xD6, 0x12, 0xE8, 0x55, 0x57, 0xCC, 0xE1, 0xB6, 0xE8, 0x83,
0xCC, 0x65, 0xB6, 0x2A, 0xEB, 0xB1, 0x7B, 0xFC, 0x6B, 0xD9, 0x62, 0x2A, 0x1B, 0xCA, 0x82, 0x93,
0x87, 0xC3, 0x73, 0x76, 0xA0, 0xF8, 0xFF, 0xB1, 0xE1, 0x5, 0x8E, 0x38, 0x27, 0x16, 0xA8, 0xD,
0xB7, 0xAA, 0xD0, 0xE8, 0x1A, 0xE6, 0xF1, 0x9E, 0x45, 0x61, 0xF2, 0xE7, 0xD2, 0x3F, 0x78, 0x92,
0xB, 0xE6, 0x6F, 0xF5, 0xA1, 0x7C, 0xC9, 0x63, 0xAB, 0x3A, 0xB7, 0x43, 0xB0, 0xA8, 0xD3, 0x9B
])
v7 = []
for i in range(0, len(cipher_bytes), 8):
chunk = cipher_bytes[i:i + 8]
value = int.from_bytes(chunk, byteorder='little')
v7.append(value)
flag = b""
for target in v7:
found = False
for i in range(0x10000):
data = i.to_bytes(2, byteorder='little')
crc = calculate_crc64_direct(data)
if crc == target:
flag += data
print(f"Found: {data.hex()} -> {hex(crc)}")
found = True
break
if not found:
print(f"Failed for {hex(target)}")
break
print("Flag:", flag.decode('latin-1'))
|